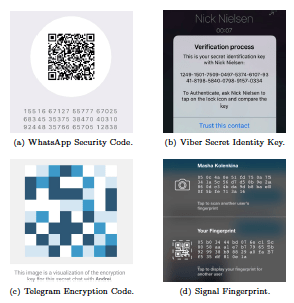
Many widely used Internet messaging and calling apps, such as WhatsApp, Viber, Telegram, and Signal, have deployed an end-to-end encryption functionality. To defeat potential manin- the-middle attackers against the key exchange protocol, the approach crucially relies upon users to perform a code verification task whereby each user must compare the code (a fingerprint of the cryptographic keys) computed by her app with the one computed by the other user’s app and reject the session if the two codes do not match. The following figure represents some of the code verification interfaces.
In this work, we study the security and usability of this human-centered code verification task for a prominent setting where the end users are remotely located, and compare it as a baseline to a potentially less frequent scenario where the end users are in close proximity. We consider several variations of the code presentation and code verification methods, incorporated into representative real-world apps, including codes encoded as numbers or images, displayed on the screen, and verbally spoken by the users. We perform a carefully-designed human factors study in a lab setting to quantify the security and usability of these different methods.
Our study results expose key weaknesses in the security and usability of the code verification methods employed in the remote end-to-end encryption apps. First, we show that generally most code verification methods offer poor security (high false accepts) and low usability (high false rejects and low user experience ratings) in the remote setting. Second, we demonstrate that, security and usability under the remote code verification setting is significantly lower than that in the proximity code verification setting. We attribute this result to the increased cognitive overhead associated with comparing the codes across two apps on the same device (remote setting) rather than across two devices (proximity setting). Overall, our work serves to highlight a serious fundamental vulnerability of Internet-based communication apps in the remote setting stemming from human errors.
People
Faculty
Student
- Maliheh Shirvanian (PhD candidate)
External Collaborators:
- Jesvin James George
Publication
- On the Pitfalls of End-to-End Encrypted Communications: A Study of Remote Key-Fingerprint Verification.
Maliheh Shirvanian, Nitesh Saxena and Jesvin James George.
In the Annual Computer Security Applications Conference (ACSAC), December 2017; arXiv preprint arXiv:1707.05285, 2017/7/17.
[pdf]