The Insider Threat of Unattended Wearables and A Defense using Audio Proximity
In this project, we highlight and study the threat arising from the unattended wearable devices pre-paired with a smartphone over a wireless communication medium. Most users may not lock their wearables due to their small form factor, and may strip themselves off of these devices often, leaving or forgetting them unattended while away from homes (or shared office spaces). An “insider” attacker (potentially a disgruntled friend, roommate, colleague, or even a spouse) can therefore get hold of the wearable, take it near the user’s phone (i.e., within radio communication range) at another location (e.g., user’s office), and surreptitiously use it across physical barriers for various nefarious purposes, including pulling and learning sensitive information from the phone (such as messages, photos or emails), and pushing sensitive commands to the phone (such as making phone calls, sending text messages and taking pictures). The attacker can then safely restore the wearable, wait for it to be left unattended again and may repeat the process for maximum impact, while the victim remains completely oblivious to the ongoing attack activity. This malicious behavior is in sharp contrast to the threat of stolen wearables where the victim would unpair the wearable as soon as the theft is detected. Considering the severity of this threat, we also respond by building a defense based on audio proximity, which limits the wearable to interface with the phone only when it can pick up on an active audio challenge produced by the phone.
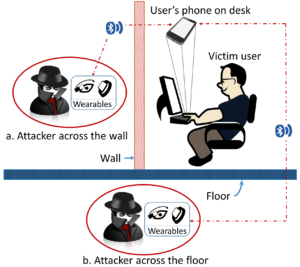
HAW attack example scenarios. An attacker with an unattended wearable comes in the Bluetooth range of the phone while being hidden across physical barriers, e.g., (a) wall, and (b) floor.
People
Faculty
Student
- Prakash Shrestha (PhD student)
- Babins Shrestha (@UAB; PhD 2016; now Cybersecurity Professional at Visa)
Publication
- Home Alone: The Insider Threat of Unattended Wearables and A Defense using Audio Proximity.
Prakash Shrestha, Babins Shrestha, and Nitesh Saxena.
To appear in IEEE Conference on Communications and Network Security (CNS), May/June 2018.
[pdf]